Documentation Index
Fetch the complete documentation index at: https://docs.cloud.coinbase.com/llms.txt
Use this file to discover all available pages before exploring further.
Overview
CDP Wallets are protected by a Trusted Execution Environment (TEE), a highly isolated compute environment for sensitive cryptographic operations such as private key generation and transaction signing. The TEE runs on AWS Nitro Enclaves, with no persistent storage, no interactive access, and no external networking. This means even root or admin users cannot access or SSH into the enclave. Private key operations happen inside the enclave boundary and are not externally accessible to CDP, AWS, or other infrastructure components.TEE architecture
The following diagram shows the TEE architecture: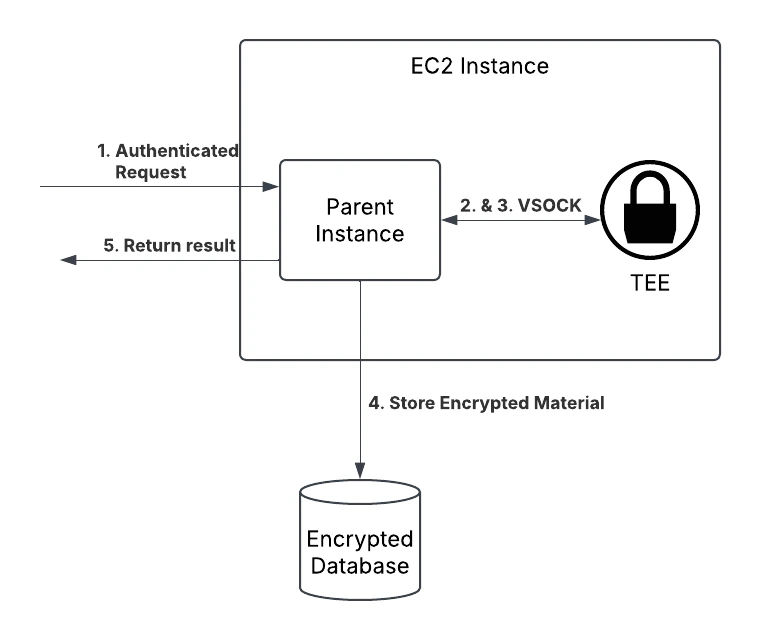
How it works
- Incoming requests are authenticated with wallet credentials:
- API key authentication uses a developer-managed Wallet Secret.
- End-user authentication uses a Temporary Wallet Secret.
- After request validation, payloads are forwarded to the enclave over VSOCK, the only data path to and from the enclave.
- The enclave performs sensitive operations, including auth signature verification, private key generation, and transaction signing. Private keys are encrypted/decrypted inside the enclave and never leave the enclave in plaintext.
- The resulting payload is sent back over VSOCK.
- The CDP API returns the result to the client.
Wallet authentication credentials
Wallet credentials are used to authorize requests to CDP Wallets. These credentials are asymmetric private keys based on ECDSA using the secp256r1 (P-256) elliptic curve. There are two credential types:- Temporary Wallet Secret (end-user auth): Device-specific key material generated and stored locally on end-user devices.
- Wallet Secret (API key auth): Developer-managed, rotatable key material used for backend-authorized operations.
For end-user wallet lifecycle and UX guidance, see Non-custodial Wallets: Overview. Temporary Wallet Secrets play the same request-authentication role for end-user auth that Wallet Secrets play for API key auth.
2FA for API key authentication
To strengthen protection for developer-managed credentials, enable two-factor authentication (2FA). Supported methods include physical security keys, passkeys, authenticator apps, security push notifications, and trusted contacts.Lost access
If you lose access to a developer-managed Wallet Secret, delete the old secret and generate a new one in CDP Portal. See Wallet Secret Rotation for full recovery and rotation steps.Compliance
CDP Wallets are built on Coinbase’s trusted, compliant crypto infrastructure, helping enterprises meet regulatory requirements out of the box.OFAC sanctions screening
All transfers are automatically screened against the OFAC sanctions list. Transfers to sanctioned addresses are blocked before they are submitted onchain, with no additional integration work required. This built-in compliance makes CDP Wallets well-suited for enterprise use cases including banks, brokerages, payment service providers, fintechs, and other regulated institutions that require robust compliance controls as a foundation.What to read next
- Authentication Methods: Learn when to use API key auth vs end-user auth.
- Non-custodial Wallets: Overview: Learn the end-user wallet model and Temporary Wallet Secrets.